Executive summary
Enterprise buyers now evaluate one system across three dimensions at once: cybersecurity, privacy, and AI governance. Pro5 is designed to meet that combined bar through enterprise security controls, privacy-by-design data handling, and AI decision-support guardrails for hiring workflows.
Across the platform, Pro5 applies enterprise controls including encryption at rest and in transit, role-based access control, comprehensive audit logging, secure software development and change management, incident response, and business continuity planning. Privacy controls include data minimization, retention and deletion workflows, DSAR support, lawful transfer mechanisms, and dedicated regional deployment options where needed.
For AI-enabled hiring workflows, Pro5 treats human oversight as a core control. The platform excludes sensitive and potentially bias-inducing attributes from live decisioning, is not designed to derive or consider them for that purpose, and provides structured explanations and review paths rather than autonomous employment decisions. Relevant hiring use cases have been independently audited under a NYC Local Law 144 bias-audit framework, and Pro5 maintains provider-side EU AI Act readiness materials for high-risk employment AI.

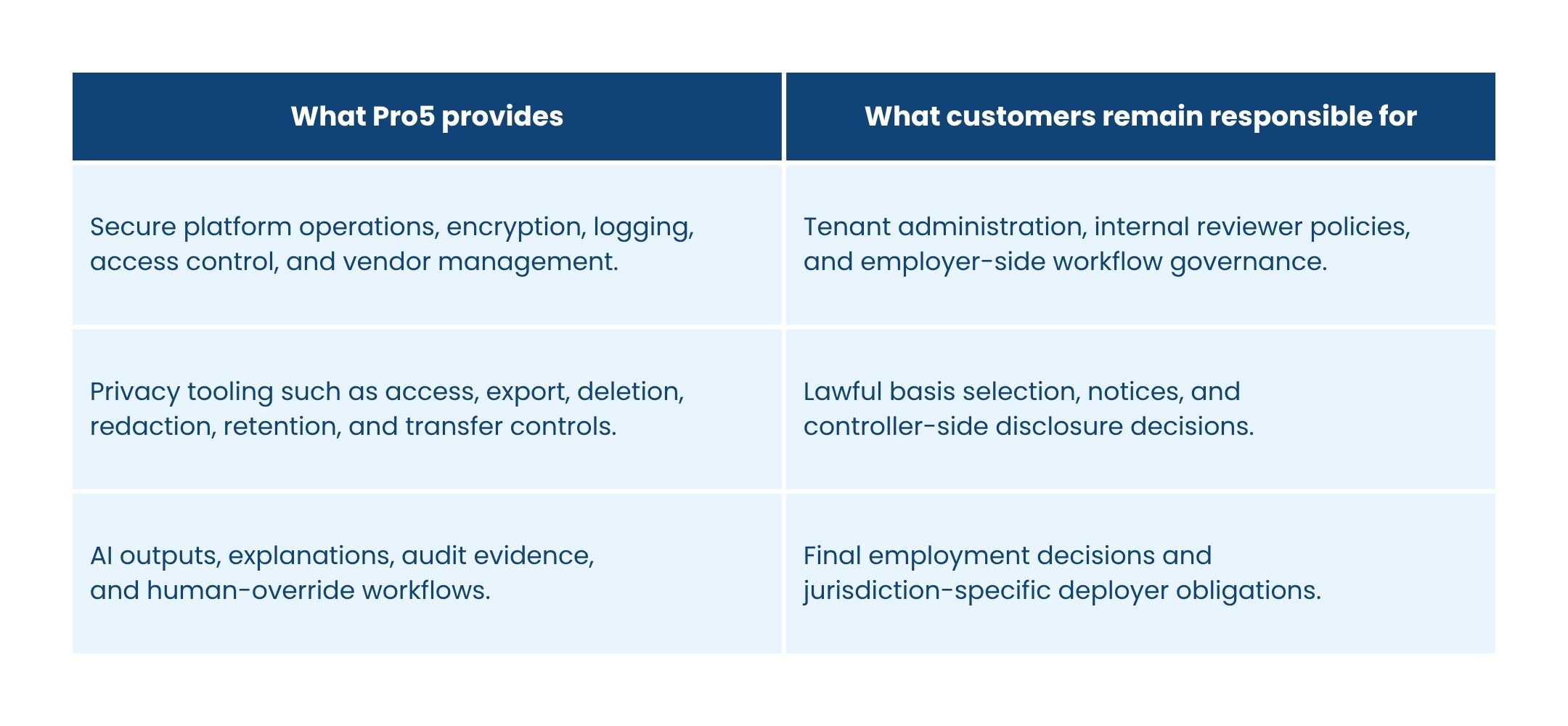
Shared-responsibility model
1. Enterprise cybersecurity foundations
Pro5's security program is designed around defense in depth and continuous control monitoring. It combines cloud and application safeguards with operational governance so that security is not a one-time review, but an ongoing discipline across the product lifecycle.
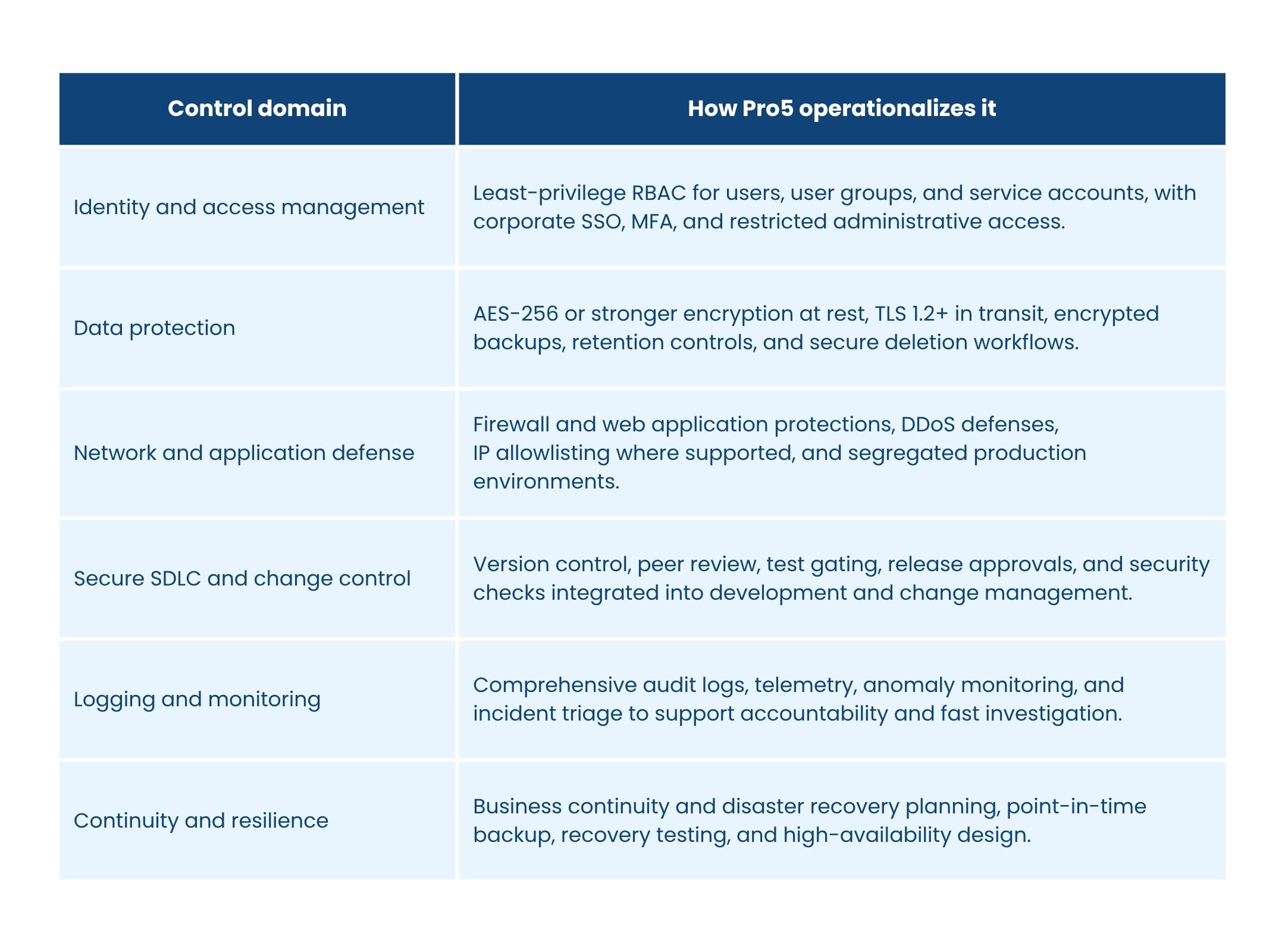
Core control domains
Enterprise deployment flexibility
Where customers need tighter isolation, Pro5 can support dedicated infrastructure, dedicated country or region-specific data storage, API-based workflows, and integration with enterprise identity and governance processes.
Framework alignment
This operating model is consistent with the NIST Cybersecurity Framework's identify, protect, detect, respond, and recover lifecycle and is reinforced through internal governance, risk reviews, and external security assessments.
2. Privacy program and global regulatory alignment
Pro5 applies privacy by design and privacy by default across collection, processing, storage, access, and deletion. The program emphasizes purpose limitation, data minimization, transparent notices, controlled retention, and support for individual rights.
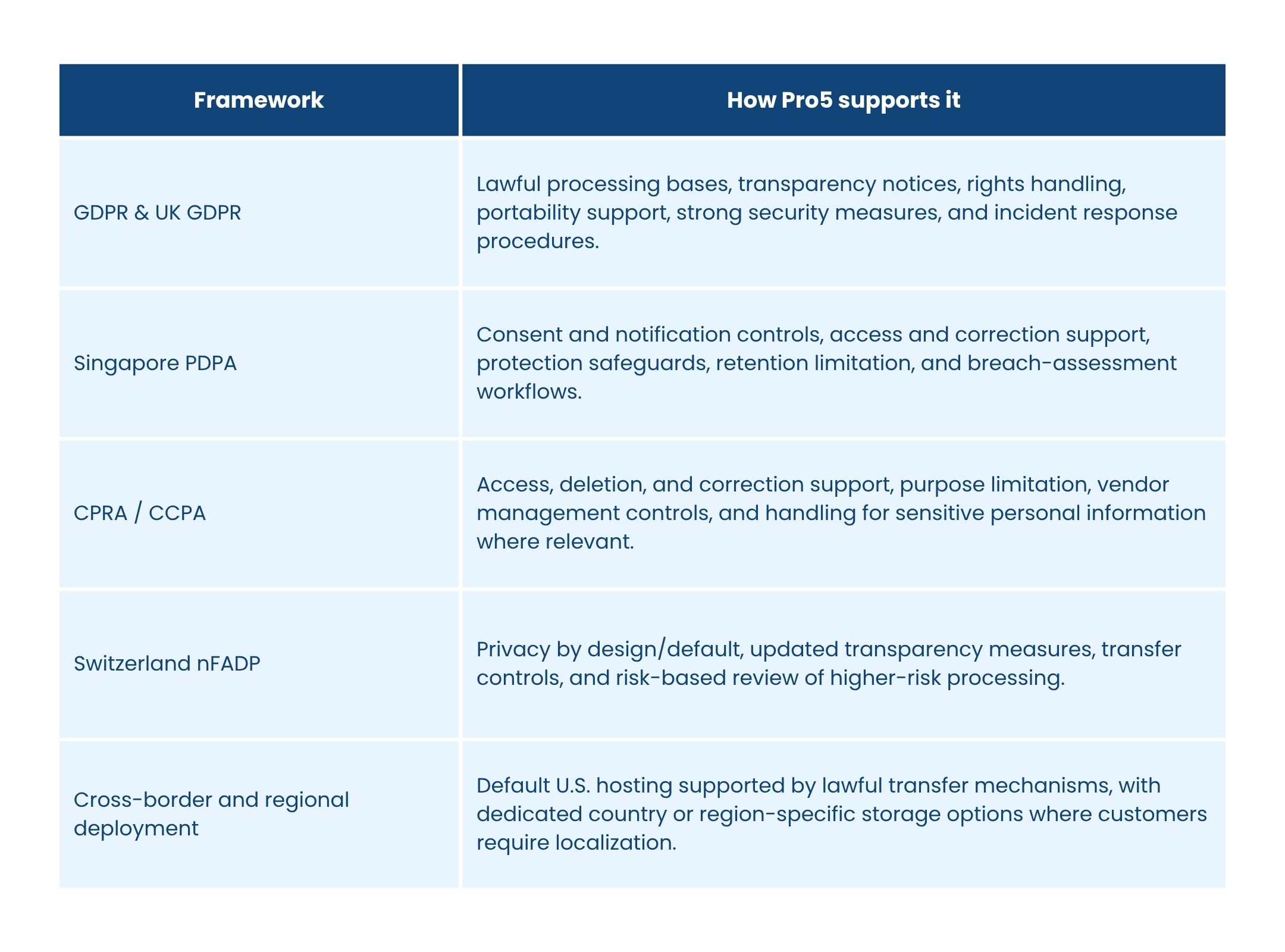
Key frameworks
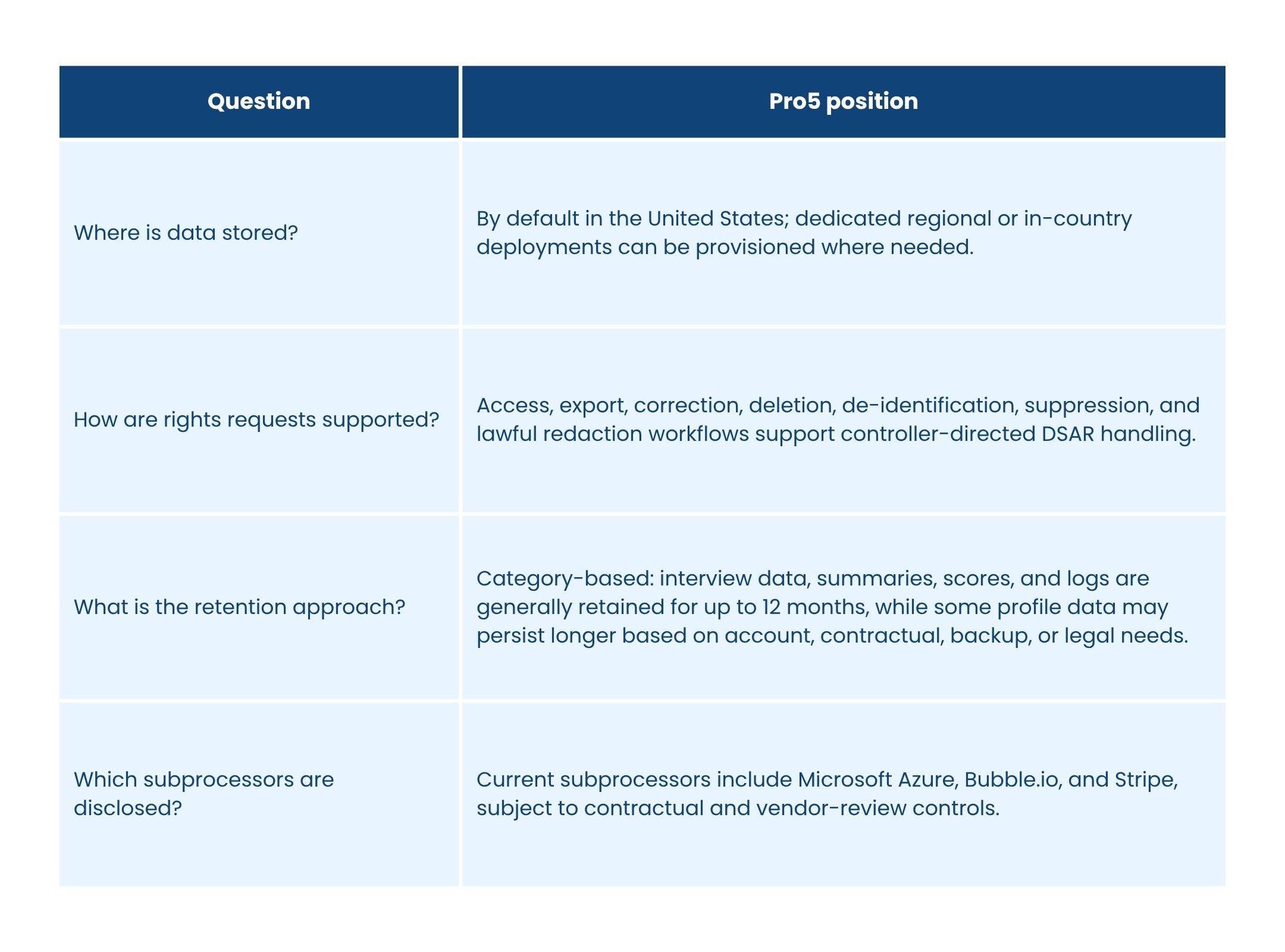
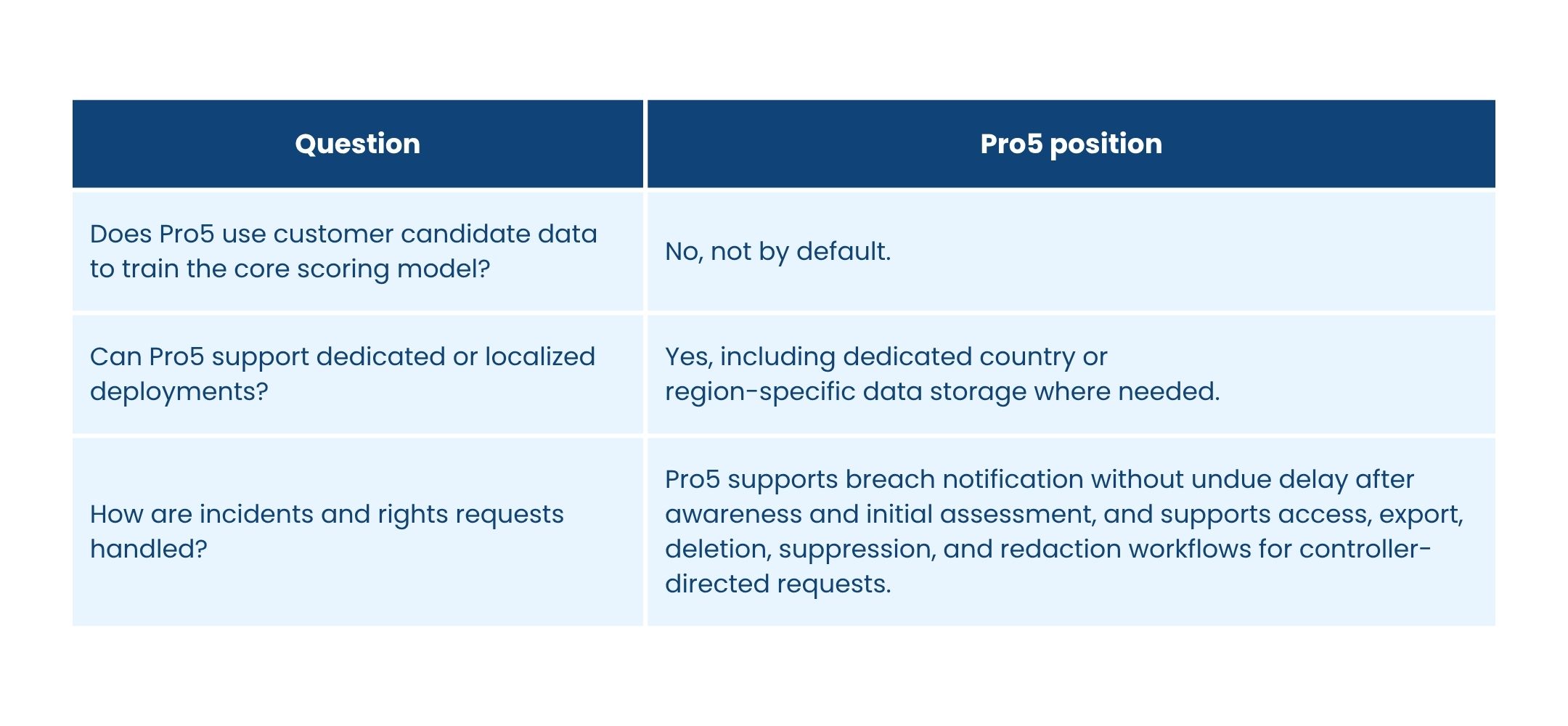
Diligence quick answers
3. AI governance in hiring
Cybersecurity and privacy are necessary, but not sufficient, for hiring AI. Pro5 also governs how AI outputs are produced, how humans review them, and which kinds of data and inferences are expressly kept out of bounds.
Core AI governance principles
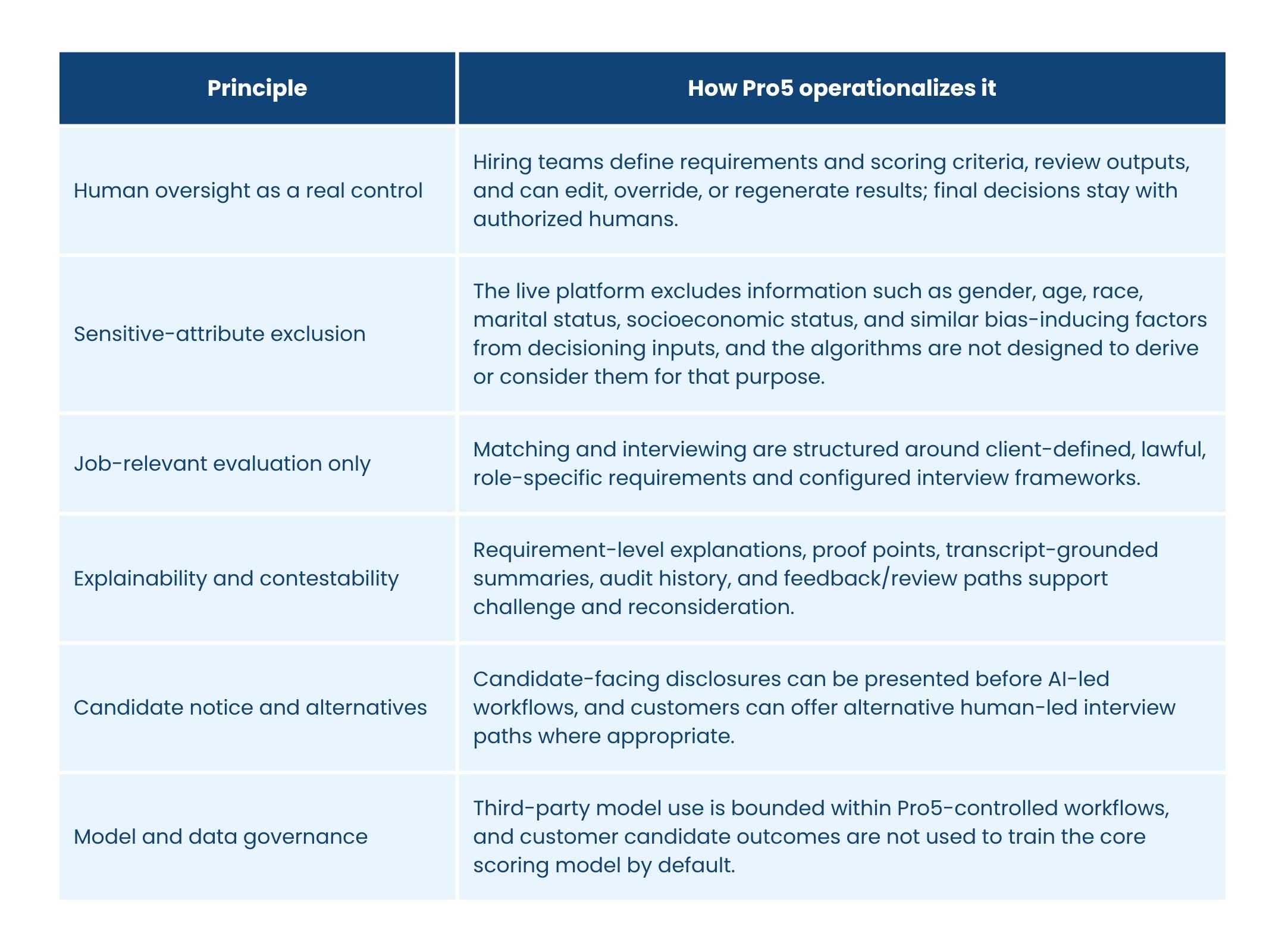
Important product boundary
Pro5 is not intended or configured to autonomously make hiring decisions, to rank candidates on protected attributes, or to perform emotion inference in workplace contexts.
Why this matters
This operating model reduces automation bias risk, improves auditability, and gives enterprise customers clearer evidence for procurement, legal, and human-review workflows.
4. NYC Local Law 144 support
For relevant hiring use cases, Pro5 has completed an independent fairness and bias audit aligned to the bias-audit framework used for NYC Local Law 144. The audit examined both AI job matching and AI interviewing in the context of candidate assessment for a specific role.
Audit scope and method
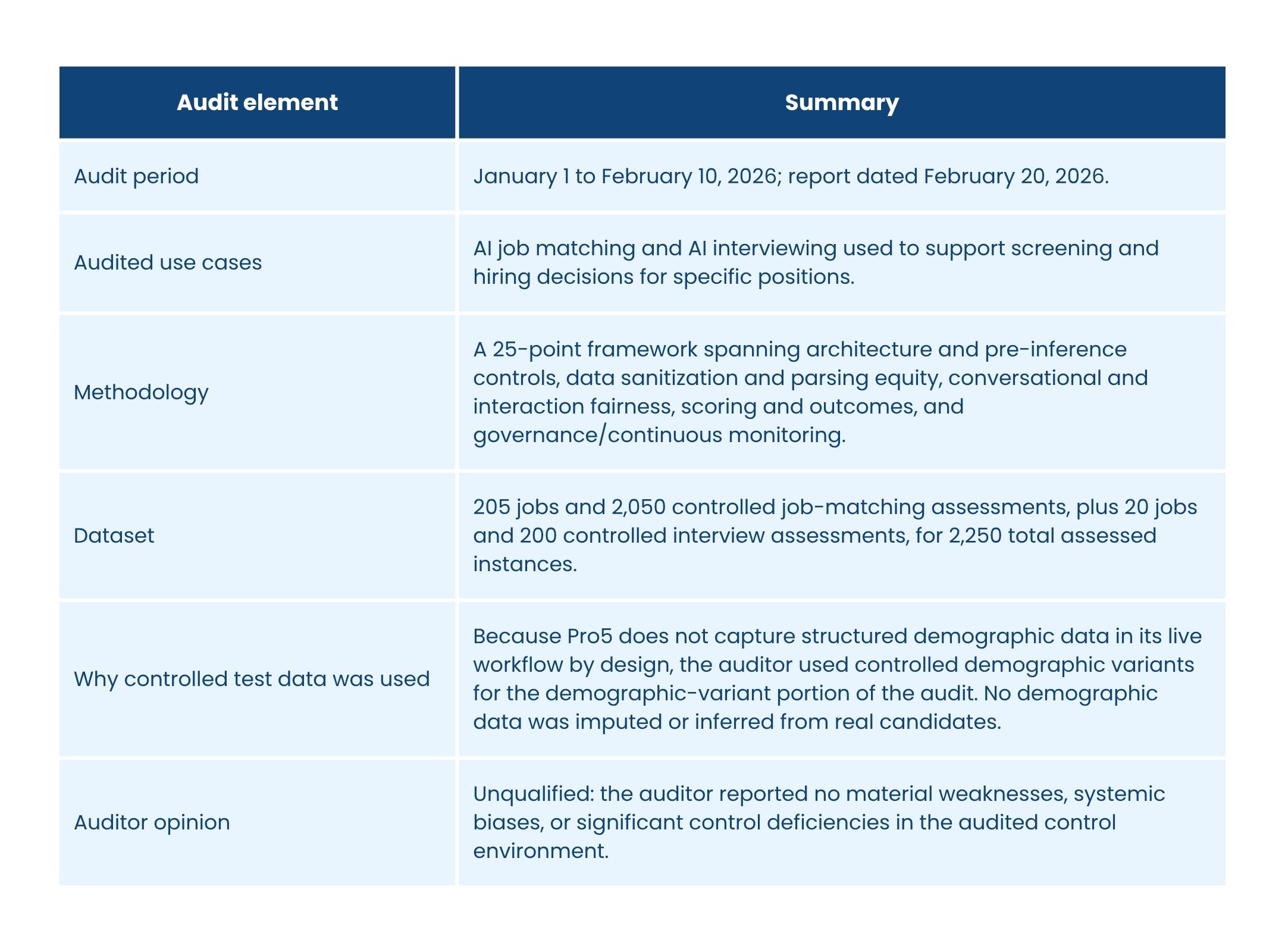
Use note
Local Law 144 also places obligations on employers and employment agencies, including use-specific notice and publication requirements when the law applies. Pro5 provides supporting evidence, explanations, and audit materials, but customers remain responsible for their own deployment-specific legal duties.
5. EU AI Act readiness
Pro5 has prepared provider-side technical documentation and governance materials to support the EU AI Act framework for high-risk employment AI. The current posture is a structured readiness program built around the provider obligations relevant to hiring-related AI systems.
Readiness areas
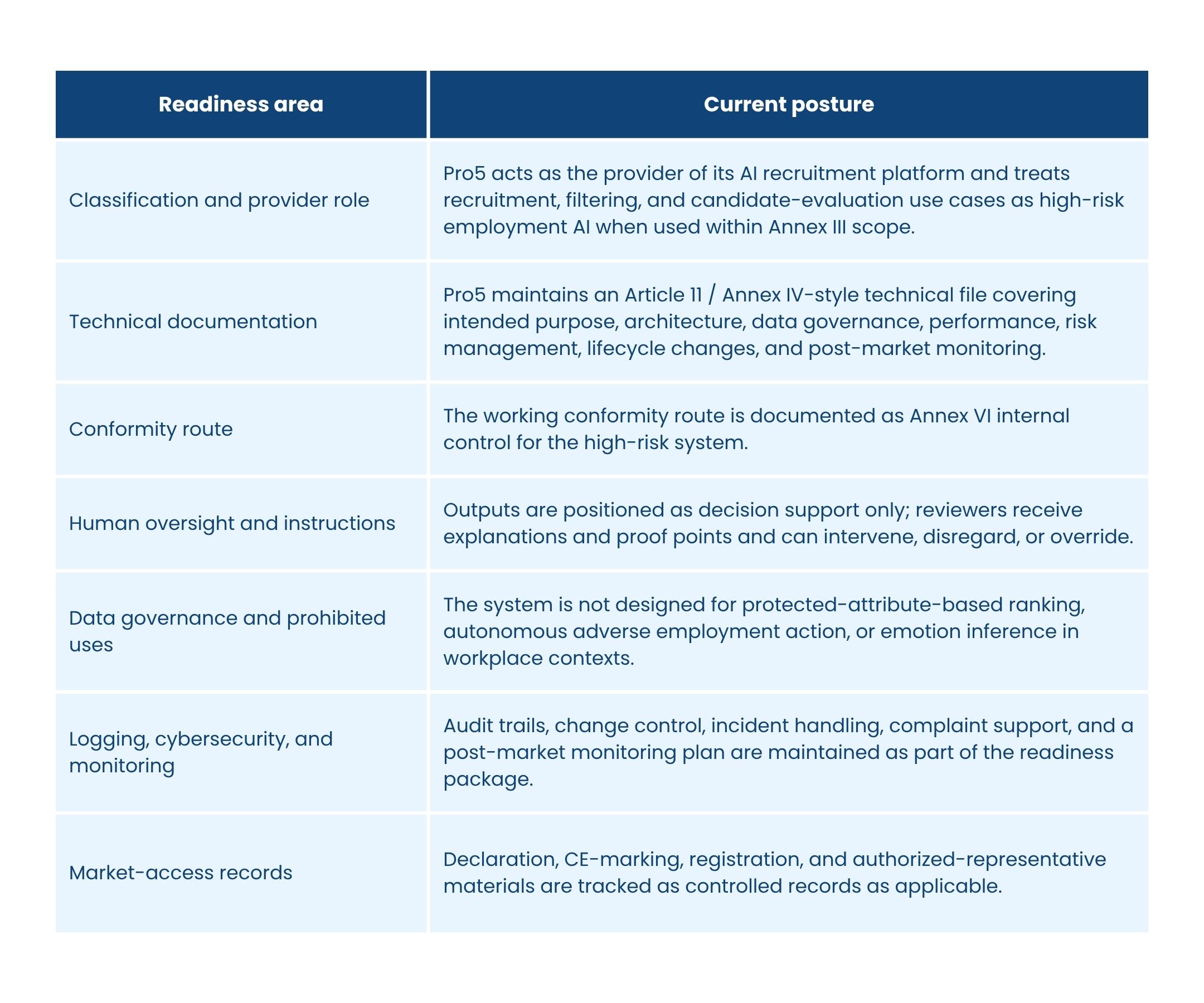
Readiness in practice
This readiness posture is designed to shorten enterprise diligence cycles and provide a structured basis for later conformity and market-access steps. Customer/deployer obligations still depend on deployment context, jurisdiction, and use.
What it means for enterprise buyers
For procurement, legal, and security teams, this means Pro5 can support AI diligence with more than product claims alone: the platform is backed by a documented system description, risk and governance structure, human-oversight model, and lifecycle monitoring plan.
6. External validation and enterprise due diligence
Pro5 supports vendor review with a combination of third-party validations, controlled documentation, and operational transparency. The goal is to reduce rework during enterprise security, privacy, and AI diligence.
Validation and evidence
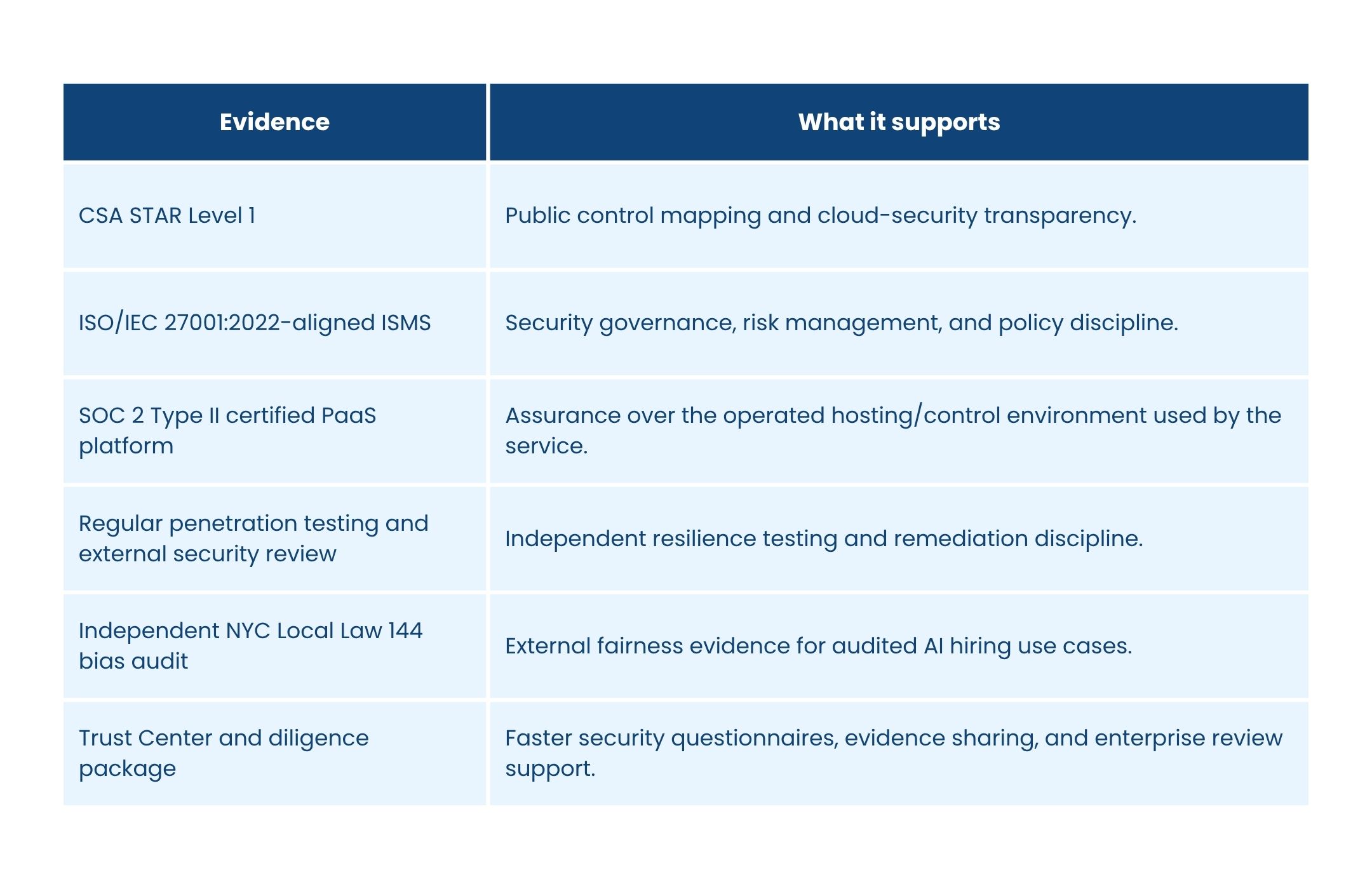
Quick answers for security and procurement teams
Taken together, these controls give enterprise buyers a clearer answer to a familiar question: can this platform meet both classic cybersecurity review and newer AI governance review? Pro5'sposition is yes - with documented controls, independent evidence, and human-centered operating boundaries.
Source basis and scope note
This refreshed whitepaper summarizes Pro5's published Enterprise Cybersecurity & Compliance Whitepaper, enterprise due diligence responses, independent bias-audit materials, and provider-side EU AI Act technical documentation. It is intended as an external summary and does not replace customer-specific legal advice ordeployment-specific compliance analysis.

